[DETECTION] Chinese ELF Packer "XMProtect"
Site - http://www.xmprotect.com/
Possible Sample ( Not 100% sure ) : https://virustotal.com/gui/file/ef4072022da954402ba6a6c0a9ac74384a5eb1d9f0e43a98405c37badac44774
APKiD Scan -
$ apkid VM01.apk.zip
[+] APKiD 2.1.3 :: from RedNaga :: rednaga.io
[*] VM01.apk.zip!classes.dex
|-> compiler : dexlib 2.x
This is very similar to EpicVM at first glance. Maybe a copy-paste of their leaked code?
Epic probably just using XMprotect api for it. I still had old screenshot before they removed the feature
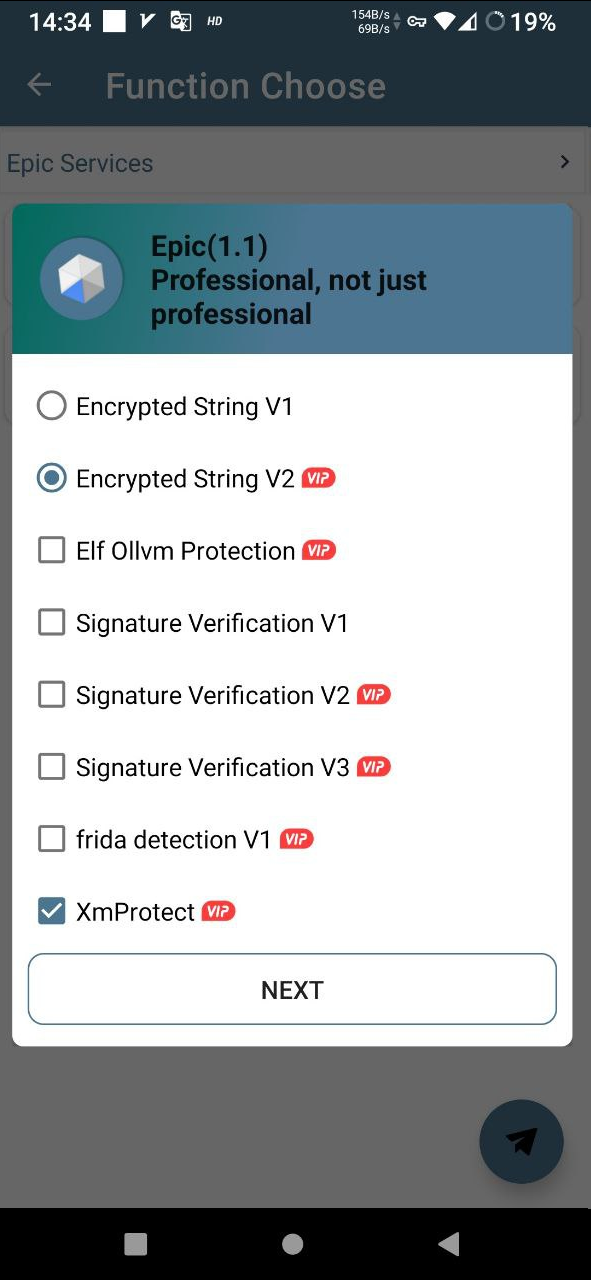
I have been using XM since 2020 so I know they have been on for long time before Epic existed
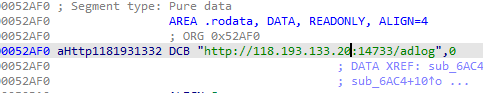
You can identify XM by checking adlog string (the IP has been changed in the new sample below)
One Epic_Vm sample which contains XMProtect MyApp.apk.zip
Another chinese application contains XMProtect CNFIX-3.8.0(22110818).apk.zip
It'd be great to have this protector included in APKiD. Any problem so far to write a rule?
It'd be great to have this protector included in APKiD. Any problem so far to write a rule?
I don't think there will be a problem. You can do what you want
And as requested:
Sample 1 (libjmtrepublic.so): https://mega.nz/file/iNYXjIqb#IXNSxH6JeVPWJODQDgyEYRueFneGbeyHTON7t_Hy0Qk
Sample 2 (libHollowMade.so): https://mega.nz/file/HJQnGYIK#d4VBKotmtQ66DhqFPGPNXov3GIeDS-QmjAJtwYNosTk
Another sample (libpolarmods.so) (Armv7 only): https://www.mediafire.com/file/r3k5ykd0emvweo5/CA_VRAIMODS_%25281%2529.apk/file
Great! I will take a look at this sample when I back from my trip. Many thanks for all the INTEL provided.
More samples.
Sample 1 https://mega.nz/file/bA5n0JSI#Pb2-tXIhOKn1UiCM3Ofj4r-sdelDaEHdDo3nsiMQuEc
/assets/jiagux86 (It's not jiagu but a mod lib 🤣)
Sample 2 https://mega.nz/file/yNwkjBLS#-pBZF6khtK2dG5WNZCIi1wc4ftXgb9dnpBeXMq24Ass
/lib/xxx/libking.so
How to identify XM
- Scramble empty functions
- Random lib name (e.g. lib1678877505-6411a34185c75_20230315185148.so)
- Has adlog url (e.g, http://218.78.108.200:10001/adlog)
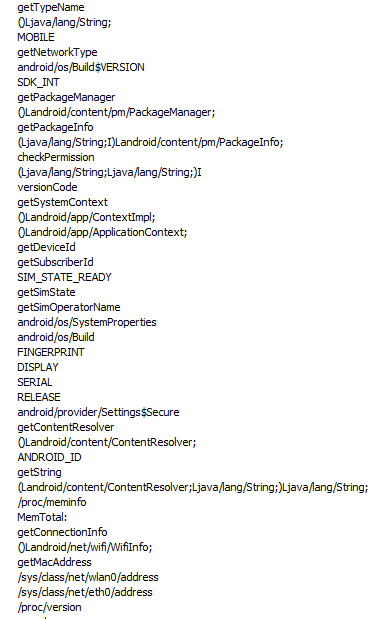
- And bunch of java APIs, probably to collect device info
More samples.
Sample 1 https://mega.nz/file/bA5n0JSI#Pb2-tXIhOKn1UiCM3Ofj4r-sdelDaEHdDo3nsiMQuEc
/assets/jiagux86(It's not jiagu but a mod lib 🤣)Sample 2 https://mega.nz/file/yNwkjBLS#-pBZF6khtK2dG5WNZCIi1wc4ftXgb9dnpBeXMq24Ass
/lib/xxx/libking.soHow to identify XM
- Scramble empty functions
- Random lib name (e.g. lib1678877505-6411a34185c75_20230315185148.so)
- Has adlog url (e.g, http://218.78.108.200:10001/adlog)
- And bunch of java APIs, probably to collect device info
Thanks a lot for all the INTEL. Would you be able to come up with a Yara rule for this packer? I can commit it later, but I am busy as hell lately.
Thanks a lot for all the INTEL. Would you be able to come up with a Yara rule for this packer? I can commit it later, but I am busy as hell lately.
I wish but I haven't learned to make Yara rule yet. I'm busy too, so no time to learn it.