Failed to load extension: Powershell @ Framework 6.2.6-dev Kali Linux install on Windows 10.0 Build 18363
Steps to reproduce
How'd you do it?
- Install Kali Linux from current latest stable rolling 2022.2 ISO image && apt update, upgrade and dist-upgrade
- meterpreter/reverse_tcp shell by msfvenom
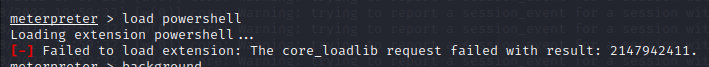
- load powershell
This section should also tell us any relevant information about the environment; for example, if an exploit that used to work is failing, tell us the victim operating system and service versions.
Were you following a specific guide/tutorial or reading documentation?
Part of the OSEP Challenge 1 machine. An OS : Windows 10 (10.0 Build 18363). Architecture : x64
Expected behavior
What should happen? The module should load
Current behavior
What happens instead? Module fails to load
Returns the following error: Failed to load extension: The core_loadlib request failed with result: 2147942411
Metasploit version
Get this with the version command in msfconsole (or git log -1 --pretty=oneline for a source install).
Additional Information
Framework: 6.2.6-dev Console : 6.2.6-dev
Information from framework.log
[07/18/2022 19:59:33] [w(0)] core: Warning: trying to report a session_event for a session with no db_record (14)
[07/18/2022 19:59:33] [w(0)] core: Warning: trying to report a session_event for a session with no db_record (14)
[07/18/2022 19:59:33] [w(0)] core: Warning: trying to report a session_event for a session with no db_record (14)
[07/18/2022 19:59:33] [w(0)] core: Warning: trying to report a session_event for a session with no db_record (14)
[07/18/2022 19:59:33] [w(0)] core: Warning: trying to report a session_event for a session with no db_record (14)
[07/18/2022 19:59:55] [w(0)] core: Warning: trying to report a session_event for a session with no db_record (14)
[07/18/2022 19:59:55] [w(0)] core: Warning: trying to report a session_event for a session with no db_record (14)
[07/18/2022 19:59:56] [w(0)] core: Warning: trying to report a session_event for a session with no db_record (14)
[07/18/2022 19:59:56] [w(0)] core: Warning: trying to report a session_event for a session with no db_record (14)
[07/18/2022 19:59:56] [e(0)] meterpreter: Failed to load extension: The core_loadlib request failed with result: 2147942411.
[07/18/2022 19:59:56] [d(0)] meterpreter: Call stack:
/usr/share/metasploit-framework/lib/rex/post/meterpreter/client_core.rb:378:in `use'
/usr/share/metasploit-framework/lib/rex/post/meterpreter/ui/console/command_dispatcher/core.rb:1337:in `block in cmd_load'
/usr/share/metasploit-framework/lib/rex/post/meterpreter/ui/console/command_dispatcher/core.rb:1307:in `each'
/usr/share/metasploit-framework/lib/rex/post/meterpreter/ui/console/command_dispatcher/core.rb:1307:in `cmd_load'
/usr/share/metasploit-framework/lib/rex/ui/text/dispatcher_shell.rb:581:in `run_command'
/usr/share/metasploit-framework/lib/rex/post/meterpreter/ui/console.rb:102:in `run_command'
/usr/share/metasploit-framework/lib/rex/ui/text/dispatcher_shell.rb:530:in `block in run_single'
/usr/share/metasploit-framework/lib/rex/ui/text/dispatcher_shell.rb:524:in `each'
/usr/share/metasploit-framework/lib/rex/ui/text/dispatcher_shell.rb:524:in `run_single'
/usr/share/metasploit-framework/lib/rex/post/meterpreter/ui/console.rb:64:in `block in interact'
/usr/share/metasploit-framework/lib/rex/ui/text/shell.rb:157:in `run'
/usr/share/metasploit-framework/lib/rex/post/meterpreter/ui/console.rb:62:in `interact'
/usr/share/metasploit-framework/lib/msf/base/sessions/meterpreter.rb:566:in `_interact'
/usr/share/metasploit-framework/lib/rex/ui/interactive.rb:53:in `interact'
/usr/share/metasploit-framework/lib/msf/ui/console/command_dispatcher/core.rb:1655:in `cmd_sessions'
/usr/share/metasploit-framework/lib/rex/ui/text/dispatcher_shell.rb:581:in `run_command'
/usr/share/metasploit-framework/lib/rex/ui/text/dispatcher_shell.rb:530:in `block in run_single'
/usr/share/metasploit-framework/lib/rex/ui/text/dispatcher_shell.rb:524:in `each'
/usr/share/metasploit-framework/lib/rex/ui/text/dispatcher_shell.rb:524:in `run_single'
/usr/share/metasploit-framework/lib/rex/ui/text/shell.rb:162:in `run'
/usr/share/metasploit-framework/lib/metasploit/framework/command/console.rb:48:in `start'
/usr/share/metasploit-framework/lib/metasploit/framework/command/base.rb:82:in `start'
/usr/bin/msfconsole:23:in `<main>'
[07/18/2022 19:59:56] [e(0)] core: Rex::RuntimeError The core_loadlib request failed with result: 2147942411.
[07/18/2022 20:06:19] [w(0)] core: Warning: trying to report a session_event for a session with no db_record (14)
[07/18/2022 20:06:19] [w(0)] core: Warning: trying to report a session_event for a session with no db_record (14)
[07/18/2022 20:06:19] [d(0)] core: HistoryManager.pop_context name: :meterpreter
[07/18/2022 20:06:22] [d(0)] core: HistoryManager.push_context name: :meterpreter
[07/18/2022 20:06:24] [w(0)] core: Warning: trying to report a session_event for a session with no db_record (8)
[07/18/2022 20:06:24] [w(0)] core: Warning: trying to report a session_event for a session with no db_record (8)
[07/18/2022 20:06:24] [w(0)] core: Warning: trying to report a session_event for a session with no db_record (8)
[07/18/2022 20:06:24] [w(0)] core: Warning: trying to report a session_event for a session with no db_record (8)
[07/18/2022 20:06:24] [e(0)] meterpreter: Failed to load extension: The core_loadlib request failed with result: 2147942411.
[07/18/2022 20:06:24] [d(0)] meterpreter: Call stack:
/usr/share/metasploit-framework/lib/rex/post/meterpreter/client_core.rb:378:in `use'
/usr/share/metasploit-framework/lib/rex/post/meterpreter/ui/console/command_dispatcher/core.rb:1337:in `block in cmd_load'
/usr/share/metasploit-framework/lib/rex/post/meterpreter/ui/console/command_dispatcher/core.rb:1307:in `each'
/usr/share/metasploit-framework/lib/rex/post/meterpreter/ui/console/command_dispatcher/core.rb:1307:in `cmd_load'
/usr/share/metasploit-framework/lib/rex/ui/text/dispatcher_shell.rb:581:in `run_command'
/usr/share/metasploit-framework/lib/rex/post/meterpreter/ui/console.rb:102:in `run_command'
/usr/share/metasploit-framework/lib/rex/ui/text/dispatcher_shell.rb:530:in `block in run_single'
/usr/share/metasploit-framework/lib/rex/ui/text/dispatcher_shell.rb:524:in `each'
/usr/share/metasploit-framework/lib/rex/ui/text/dispatcher_shell.rb:524:in `run_single'
/usr/share/metasploit-framework/lib/rex/post/meterpreter/ui/console.rb:64:in `block in interact'
/usr/share/metasploit-framework/lib/rex/ui/text/shell.rb:157:in `run'
/usr/share/metasploit-framework/lib/rex/post/meterpreter/ui/console.rb:62:in `interact'
/usr/share/metasploit-framework/lib/msf/base/sessions/meterpreter.rb:566:in `_interact'
/usr/share/metasploit-framework/lib/rex/ui/interactive.rb:53:in `interact'
/usr/share/metasploit-framework/lib/msf/ui/console/command_dispatcher/core.rb:1655:in `cmd_sessions'
/usr/share/metasploit-framework/lib/rex/ui/text/dispatcher_shell.rb:581:in `run_command'
/usr/share/metasploit-framework/lib/rex/ui/text/dispatcher_shell.rb:530:in `block in run_single'
/usr/share/metasploit-framework/lib/rex/ui/text/dispatcher_shell.rb:524:in `each'
/usr/share/metasploit-framework/lib/rex/ui/text/dispatcher_shell.rb:524:in `run_single'
/usr/share/metasploit-framework/lib/rex/ui/text/shell.rb:162:in `run'
/usr/share/metasploit-framework/lib/metasploit/framework/command/console.rb:48:in `start'
/usr/share/metasploit-framework/lib/metasploit/framework/command/base.rb:82:in `start'
/usr/bin/msfconsole:23:in `<main>'
[07/18/2022 20:06:24] [e(0)] core: Rex::RuntimeError The core_loadlib request failed with result: 2147942411.
[07/18/2022 20:08:33] [w(0)] core: Warning: trying to report a session_event for a session with no db_record (8)
[07/18/2022 20:08:33] [w(0)] core: Warning: trying to report a session_event for a session with no db_record (8)
[07/18/2022 20:08:33] [w(0)] core: Warning: trying to report a session_event for a session with no db_record (8)
[07/18/2022 20:08:33] [w(0)] core: Warning: trying to report a session_event for a session with no db_record (8)
[07/18/2022 20:08:33] [w(0)] core: Warning: trying to report a session_event for a session with no db_record (8)
[07/18/2022 20:08:33] [w(0)] core: Warning: trying to report a session_event for a session with no db_record (8)
[07/18/2022 20:08:33] [w(0)] core: Warning: trying to report a session_event for a session with no db_record (8)
[07/18/2022 20:08:33] [w(0)] core: Warning: trying to report a session_event for a session with no db_record (8)
[07/18/2022 20:09:07] [w(0)] core: Warning: trying to report a session_event for a session with no db_record (8)
[07/18/2022 20:09:11] [w(0)] core: Warning: trying to report a session_event for a session with no db_record (8)
[07/18/2022 20:09:11] [w(0)] core: Warning: trying to report a session_event for a session with no db_record (8)
[07/18/2022 20:09:11] [d(0)] core: HistoryManager.pop_context name: :meterpreter
Without access to the box this will be hard to debug. Would you mind running this again with TLV logging enabled, then provide the output?
You should be able to enable the logging with setg SessionTlvLogging true
https://docs.metasploit.com/docs/using-metasploit/advanced/meterpreter/meterpreter-debugging-meterpreter-sessions.html#log-meterpreter-tlv-packets
Thanks for the swift response. Here is the result:
msf6 exploit(multi/handler) >
msf6 exploit(multi/handler) >
[*] Sending stage (200774 bytes) to 192.168.186.122
SEND: #<Rex::Post::Meterpreter::Packet type=Request tlvs=[
#<Rex::Post::Meterpreter::Tlv type=COMMAND_ID meta=INT value=16 command=core_negotiate_tlv_encryption>
#<Rex::Post::Meterpreter::Tlv type=REQUEST_ID meta=STRING value="99368913999885322410651186866658">
#<Rex::Post::Meterpreter::Tlv type=RSA_PUB_KEY meta=RAW value="0\x82\x01\"0\r\x06\t*\x86H\x86\xF7\r\x01\x01\x01\ ...">
]>
RECV: #<Rex::Post::Meterpreter::Packet type=Response tlvs=[
#<Rex::Post::Meterpreter::Tlv type=COMMAND_ID meta=INT value=16 command=core_negotiate_tlv_encryption>
#<Rex::Post::Meterpreter::Tlv type=REQUEST_ID meta=STRING value="99368913999885322410651186866658">
#<Rex::Post::Meterpreter::Tlv type=SYM_KEY_TYPE meta=INT value=1>
#<Rex::Post::Meterpreter::Tlv type=ENC_SYM_KEY meta=RAW value="m\xB9RZF\xD2\x0EK\x11g\xD5\x11\a3\x9BJ\x7F\xAB\x8 ...">
#<Rex::Post::Meterpreter::Tlv type=RESULT meta=INT value=0>
#<Rex::Post::Meterpreter::Tlv type=UUID meta=RAW value="\xE3\x9E\x02\x1A?@\xAA!;\x88:\x8AY^^,">
]>
SEND: #<Rex::Post::Meterpreter::Packet type=Request tlvs=[
#<Rex::Post::Meterpreter::Tlv type=COMMAND_ID meta=INT value=10 command=core_enumextcmd>
#<Rex::Post::Meterpreter::Tlv type=REQUEST_ID meta=STRING value="52656391752038725345219535541370">
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=0>
#<Rex::Post::Meterpreter::Tlv type=LENGTH meta=INT value=1000>
]>
RECV: #<Rex::Post::Meterpreter::Packet type=Response tlvs=[
#<Rex::Post::Meterpreter::Tlv type=COMMAND_ID meta=INT value=10 command=core_enumextcmd>
#<Rex::Post::Meterpreter::Tlv type=REQUEST_ID meta=STRING value="52656391752038725345219535541370">
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=17 command=core_patch_url>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=19 command=core_pivot_remove>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=18 command=core_pivot_add>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=22 command=core_set_uuid>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=21 command=core_set_session_guid>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=11 command=core_get_session_guid>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=13 command=core_machine_id>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=10 command=core_enumextcmd>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=12 command=core_loadlib>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=23 command=core_shutdown>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=14 command=core_migrate>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=30 command=core_transport_remove>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=24 command=core_transport_add>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=29 command=core_transport_prev>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=28 command=core_transport_next>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=25 command=core_transport_change>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=33 command=core_transport_sleep>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=27 command=core_transport_list>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=31 command=core_transport_setcerthash>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=26 command=core_transport_getcerthash>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=32 command=core_transport_set_timeouts>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=16 command=core_negotiate_tlv_encryption>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=3 command=core_channel_interact>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=7 command=core_channel_tell>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=2 command=core_channel_eof>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=6 command=core_channel_seek>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=5 command=core_channel_read>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=1 command=core_channel_close>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=8 command=core_channel_write>
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=4 command=core_channel_open>
#<Rex::Post::Meterpreter::Tlv type=RESULT meta=INT value=0>
#<Rex::Post::Meterpreter::Tlv type=UUID meta=RAW value="\xE3\x9E\x02\x1A?@\xAA!;\x88:\x8AY^^,">
]>
SEND: #<Rex::Post::Meterpreter::Packet type=Request tlvs=[
#<Rex::Post::Meterpreter::Tlv type=COMMAND_ID meta=INT value=2 command=core_channel_eof>
#<Rex::Post::Meterpreter::Tlv type=REQUEST_ID meta=STRING value="82106715632477904177963030265601">
#<Rex::Post::Meterpreter::Tlv type=CHANNEL_ID meta=INT value=0>
]>
RECV: #<Rex::Post::Meterpreter::Packet type=Response tlvs=[
#<Rex::Post::Meterpreter::Tlv type=COMMAND_ID meta=INT value=2 command=core_channel_eof>
#<Rex::Post::Meterpreter::Tlv type=REQUEST_ID meta=STRING value="82106715632477904177963030265601">
#<Rex::Post::Meterpreter::Tlv type=BOOL meta=BOOL value=false>
#<Rex::Post::Meterpreter::Tlv type=RESULT meta=INT value=1168>
#<Rex::Post::Meterpreter::Tlv type=UUID meta=RAW value="\xC2#\x9A\x90y\xD8J[\x9F\xD4\x9E\xD6\xFD\x01q\xC1 ...">
]>
[*] Meterpreter session 17 opened (192.168.49.186:443 -> 192.168.186.122:50146) at 2022-07-19 04:05:03 -0400
sessions -i 17
[*] Starting interaction with 17...
meterpreter > load powershell
Loading extension powershell...
SEND: #<Rex::Post::Meterpreter::Packet type=Request tlvs=[
#<Rex::Post::Meterpreter::Tlv type=COMMAND_ID meta=INT value=10 command=core_enumextcmd>
#<Rex::Post::Meterpreter::Tlv type=REQUEST_ID meta=STRING value="78789572323942047914820860550911">
#<Rex::Post::Meterpreter::Tlv type=UINT meta=INT value=14000>
#<Rex::Post::Meterpreter::Tlv type=LENGTH meta=INT value=1000>
]>
RECV: #<Rex::Post::Meterpreter::Packet type=Response tlvs=[
#<Rex::Post::Meterpreter::Tlv type=COMMAND_ID meta=INT value=10 command=core_enumextcmd>
#<Rex::Post::Meterpreter::Tlv type=REQUEST_ID meta=STRING value="78789572323942047914820860550911">
#<Rex::Post::Meterpreter::Tlv type=RESULT meta=INT value=0>
#<Rex::Post::Meterpreter::Tlv type=UUID meta=RAW value="\xE3\x9E\x02\x1A?@\xAA!;\x88:\x8AY^^,">
]>
SEND: #<Rex::Post::Meterpreter::Packet type=Request tlvs=[
#<Rex::Post::Meterpreter::Tlv type=COMMAND_ID meta=INT value=12 command=core_loadlib>
#<Rex::Post::Meterpreter::Tlv type=REQUEST_ID meta=STRING value="35018696030200158848857431941658">
#<Rex::Post::Meterpreter::Tlv type=DATA meta=RAW value="MZ\x90\x00\x03\x00\x00\x00\x04\x00\x00\x00\xFF\xF ...">
#<Rex::Post::Meterpreter::Tlv type=LIBRARY_PATH meta=STRING value="ext572315.x64.dll">
#<Rex::Post::Meterpreter::Tlv type=FLAGS meta=INT value=2>
#<Rex::Post::Meterpreter::Tlv type=TARGET_PATH meta=STRING value="/tmp/ext572315.x64.dll">
]>
SEND: #<Rex::Post::Meterpreter::Packet type=Request tlvs=[
#<Rex::Post::Meterpreter::Tlv type=COMMAND_ID meta=INT value=2 command=core_channel_eof>
#<Rex::Post::Meterpreter::Tlv type=REQUEST_ID meta=STRING value="81541405022051715363378159110547">
#<Rex::Post::Meterpreter::Tlv type=CHANNEL_ID meta=INT value=0>
]>
RECV: #<Rex::Post::Meterpreter::Packet type=Response tlvs=[
#<Rex::Post::Meterpreter::Tlv type=COMMAND_ID meta=INT value=2 command=core_channel_eof>
#<Rex::Post::Meterpreter::Tlv type=REQUEST_ID meta=STRING value="81541405022051715363378159110547">
#<Rex::Post::Meterpreter::Tlv type=BOOL meta=BOOL value=false>
#<Rex::Post::Meterpreter::Tlv type=RESULT meta=INT value=1168>
#<Rex::Post::Meterpreter::Tlv type=UUID meta=RAW value="\xCB\xF9\xF3O\xF9e\x92\x1Cy\xB0x\xB2\ee\x89K">
]>
RECV: #<Rex::Post::Meterpreter::Packet type=Response tlvs=[
#<Rex::Post::Meterpreter::Tlv type=COMMAND_ID meta=INT value=12 command=core_loadlib>
#<Rex::Post::Meterpreter::Tlv type=REQUEST_ID meta=STRING value="35018696030200158848857431941658">
#<Rex::Post::Meterpreter::Tlv type=RESULT meta=INT value=2147942411>
#<Rex::Post::Meterpreter::Tlv type=UUID meta=RAW value="\xE3\x9E\x02\x1A?@\xAA!;\x88:\x8AY^^,">
]>
[-] Failed to load extension: The core_loadlib request failed with result: 2147942411.
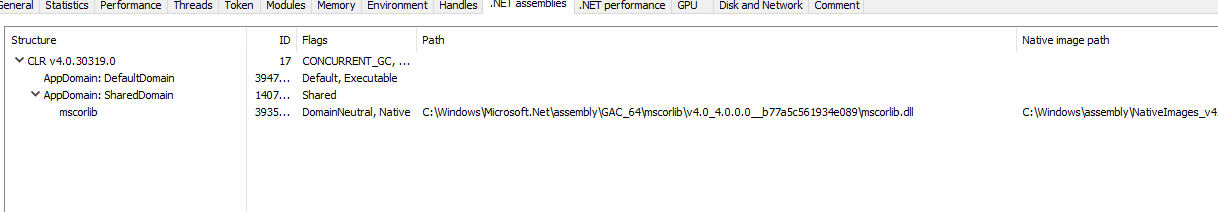
Also got this problem on MSF 6.2.7-dev and meterpreter tested on Windows 10 v21H2 Build 19044.1865. The CLR seems loaded tho.
Hi!
This issue has been left open with no activity for a while now.
We get a lot of issues, so we currently close issues after 60 days of inactivity. It’s been at least 30 days since the last update here. If we missed this issue or if you want to keep it open, please reply here. You can also add the label "not stale" to keep this issue open!
As a friendly reminder: the best way to see this issue, or any other, fixed is to open a Pull Request.
Hi again!
It’s been 60 days since anything happened on this issue, so we are going to close it. Please keep in mind that I’m only a robot, so if I’ve closed this issue in error please feel free to reopen this issue or create a new one if you need anything else.
As a friendly reminder: the best way to see this issue, or any other, fixed is to open a Pull Request.
It could be because your Windows 10 didn't turn off Windows Defender. I got the same error before I closed Windows Defender, but when I closed Windows Defender, I successfully execute "load powershell".